Nova Prism Start 425-635-2970 Unlocking Caller Verification
Nova Prism Start 425-635-2970 introduces a structured approach to caller verification, balancing security with governance. It outlines layered checks, cryptographic tokens, and risk signals to confirm identity before permitting sensitive actions. The framework emphasizes auditable controls, regulatory alignment, and data provenance, while avoiding exposure of sensitive data. Practical steps and potential pitfalls are identified to guide implementation, leaving a decisive question about its impact on risk management and access control for stakeholders.
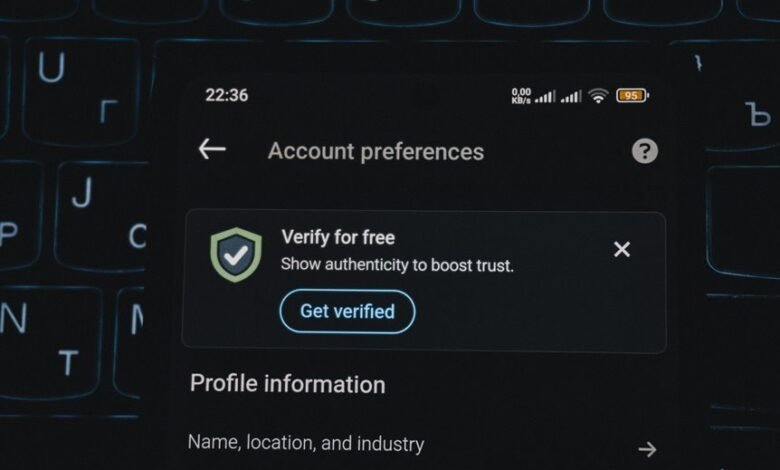
What Is Caller Verification and Why It Matters
Caller verification is a security measure that confirms the identity of a caller before granting access to sensitive information or initiating actions. It elevates accountability, reduces fraud, and supports compliance with regulatory frameworks. In business security terms, robust verification processes deter impersonation and data breaches, enabling controlled information flow while preserving user autonomy and freedom within auditable, transparent procedures.
How Nova Prism Start 425-635-2970 Works Behind the Scenes
Nova Prism Start 425-635-2970 operates through a layered verification framework that discloses its internal processes without exposing sensitive data. In practice, Nova Prism analyzes call metadata, cryptographic tokens, and risk signals behind the scenes; this clarifies how Caller verification maintains trust.
The importance lies in transparent governance, auditable controls, and consistent enforcement of regulatory standards for user freedom.
Practical Steps to Enable Verified Calls for Your Business
Practical steps to enable verified calls for a business begin with a formal assessment of communication channels and regulatory requirements, followed by the configuration of identity verification protocols.
The process identifies suitable verification methods and establishes interfaces with carriers and messaging platforms.
A rigorous risk assessment informs control choices, data handling, and auditability, ensuring compliant, verifiable caller identities without compromising operational freedom.
Common Pitfalls and How to Avoid Them in Verification
Effective verification programs often stumble on misconfigurations, reliance on single-factor controls, and inconsistent data sources, all of which can undermine trust and create regulatory exposure.
The discussion highlights verification pitfalls and emphasizes best practices, such as multi-factor approaches, periodic audits, and data provenance.
Adherence to standards reduces risk while preserving caller autonomy and regulatory compliance in a freedom-friendly governance framework.
Conclusion
In regulated environments, verified caller verification acts as a trusted gatekeeper, much like a security checkpoint at a critical facility. A single incident—where a breach was halted by a tokenized credential—demonstrates the system’s value: metadata, tokens, and risk signals work together to prove identity without exposing sensitive data. The result is auditable governance, reduced fraud, and compliant information flow, enabling safer, accountable access for sensitive actions.




