Account Data Review – 8888708842, 3317586838, 3519371931, Dtyrjy, 3792753351
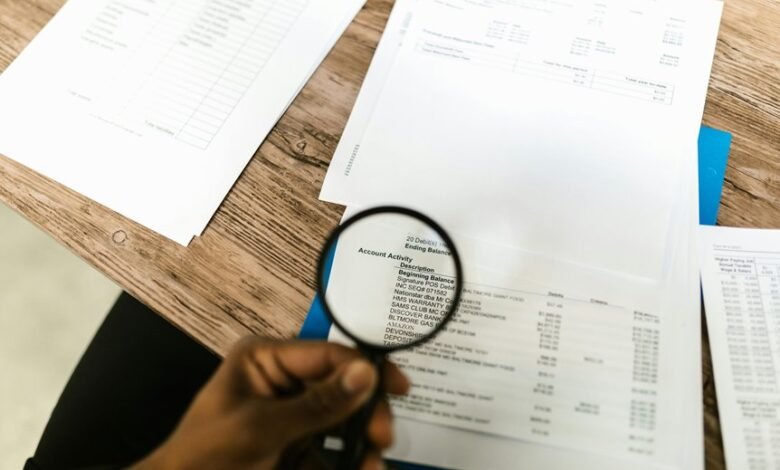
The account data review for 8888708842, 3317586838, 3519371931, Dtyrjy, and 3792753351 proceeds with disciplined scrutiny of logs, access events, and profile attributes. Signals are traced against baselines with careful reconciliation and provenance checks. Noise is filtered to preserve critical context, while anomalies are documented for transparent action. The process emphasizes auditable steps and minimal disruption, leaving a clear impetus to continue examining how each identifier aligns with established integrity standards.
What Account Data Review Reveals About ID 8888708842
The account data review for ID 8888708842 is conducted with exacting scrutiny, focusing on the integrity and consistency of transactional logs, access events, and profile attributes.
The assessment identifies discrete patterns in data signals, confirms alignment with documented permissions, and highlights anomalies without overinterpretation.
Findings emphasize accountability, transparency, and ongoing vigilance, supporting an autonomous, freedom-friendly governance of account data review.
account review, data signals.
Interpreting Activity and Security Signals for 3317586838
Interpreting activity and security signals for 3317586838 requires a precise, methodical approach that traces event patterns across logs, access attempts, and configuration changes. Analysts assess interpreting activity with restraint, filtering noise while preserving context.
Security signals for 3317586838 are weighed against baseline behavior, ensuring data integrity for 3317586838 remains intact, consistent, and auditable, guiding vigilant, freedom-oriented decision making.
Assessing Data Integrity Across 3519371931, Dtyrjy, and 3792753351
Assessing data integrity across 3519371931, Dtyrjy, and 3792753351 requires a disciplined, cross-system approach that traces lineage from source to present state.
The evaluation emphasizes data integrity through independent verification, reconciliation of records, and provenance checks.
Attention to security signals, anomaly detection, and tamper indicators ensures resilience, transparency, and accountability across interconnected data streams without compromising operational freedom.
Red Flags and Remediation Playbook for the Five Identifiers
To extend the prior work on data integrity across the five identifiers, the Red Flags and Remediation Playbook identifies measurable warning signs, systematic verification steps, and defined response procedures. Vigilant monitoring excludes Irrelevant tangent speculation bias, focusing on objective indicators, reproducible checks, and documented corrective actions. Clear escalation paths ensure timely remediation, minimizing disruption while preserving data provenance and user autonomy.
Frequently Asked Questions
How Often Is Account Data Review Updated for These IDS?
The review cadence for these IDs follows a formal cadence with periodic checks. Review update frequency is maintained consistently, ensuring data integrity and security. Updates occur at established intervals, reflecting a vigilant, methodical approach for ongoing account data review.
What Coverage Gaps Exist in Data Sources Used?
Data gaps exist where data sources fail to capture critical inputs, leaving blind spots in coverage. The assessment identifies missing or incomplete signals, requiring targeted enrichment of data sources to reduce risk and improve decision quality.
Are There Privacy Implications of the Review Findings?
The review reveals privacy concerns stemming from data handling practices; implications include potential exposure and misuse. Data minimization is recommended to reduce risk, ensuring only essential information is processed and stored, aligning with privacy-conscious, freedom-respecting governance.
Can Anomaly Detection Distinguish False Positives Reliably?
Anomaly detection can reduce false positives with calibrated thresholds and iterative validation. However, completeness relies on diverse data and context; independent review remains essential, as false positives may still occur, demanding continuous monitoring, auditing, and transparent criteria.
What External Data Could Enhance Validation Accuracy?
External validation could incorporate purchase history, geolocation, and device fingerprints; data enrichment would augment anomaly indicators, enabling robust cross-checks. The approach remains precise, methodical, and vigilant, while preserving audience autonomy and interpretive flexibility.
Conclusion
A meticulous, methodical motion marks maturity across the five identifiers. Data durability, detected deviations, and disciplined diligence define documented decisions. Vigilant reviews verify variances, validate provenance, and vault vulnerabilities. Patterns are parsed, provenance preserved, and possible problems promptly precipitated into remediation. Consistent calibrations, cross-checks, and conscientious corroborations confirm coherent cycles, credible controls, and careful corrections, cultivating continuous confidence. Ultimately, a measured, transparent, and traceable trail triumphs in tackling turbulence and maintaining trust.




