Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
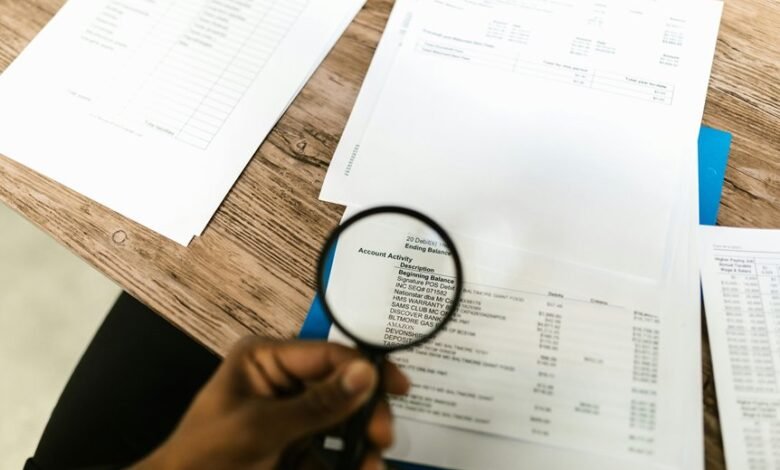
Account Data Review traces identifiers 8285431493, mez68436136, 9173980781, 7804091305, and the IP 111.90.150.204l to establish a traceable provenance trail. The analysis focuses on how identities intersect with access events, data movements, and system changes. It highlights the need for verifiable authentication, authorization, and logging. The discussion points to potential gaps and controls that shape trust and accountability, inviting the next step in a structured evaluation. The implications suggest a path forward that demands careful scrutiny.
What the Account Identifiers Mean and Why It Matters
Account identifiers are the most fundamental keys to organizing and accessing account data. The subtopic examines how identifiers enable traceability, support data provenance, and determine account access controls. Each identifier maps to a unique lineage, linking events, actions, and changes.
Understanding this framework clarifies data lineage, secures governance, and preserves freedom through transparent, auditable interactions with systems and records.
How Data Is Collected, Stored, and Monitored Safely
Data collection, storage, and monitoring practices follow from the established framework of account identifiers by ensuring that data provenance, access controls, and auditability are maintained across the full lifecycle.
The approach is precise and methodical, outlining data collection protocols, secure data storage architectures, and continuous monitoring mechanisms.
It emphasizes transparency, least privilege, and verifiable recordkeeping to support informed, freedom-oriented accountability in data handling.
Red Flags and Risk Scenarios to Watch For
Early detection of anomalies is essential for maintaining trust and integrity within account data handling; therefore, the section identifies concrete red flags and plausible risk scenarios that warrant immediate attention.
Observed irregular access patterns, unusual data transfers, and inconsistent authorization changes signal security risks.
Emphasis on access governance, data handling, and risk awareness guides rapid remediation and ongoing vigilance.
Practical Safeguards and Governance for Trustworthy Access
Recent patterns of irregular access and unexpected data movements highlighted in the prior subtopic underscore the need for concrete safeguards and structured governance.
Practical safeguards enact data governance through principled policies, auditable access controls, and continuous monitoring.
Strong authentication and role-based access minimize risk, while governance frameworks ensure accountability, transparency, and timely remediation, preserving trust and enabling responsible data sharing and use.
Frequently Asked Questions
How to Correct Misattributed Account Identifiers?
Misattribution causes are mitigated through rigorous identifier reconciliation, cross-checking source records, and auditing linkage trails. The process systematically identifies mismatches, remediates them, and documents impact, ensuring accountability and enabling correct attribution across all relevant systems.
Who Can Access the Reviewed Data and When?
Access is limited to authorized personnel with predefined roles. Access controls enforce permissions, while audit trails record each event, ensuring accountability. The policy permits reviewed data exposure only under need-to-know criteria, balancing transparency with security and freedom.
What Are the Data Retention Durations for Logs?
Data retention for logs is defined by policy: logs archival occurs after 90 days, with access restricted to authorized personnel; retention durations may extend to 365 days for compliance, while anonymized data may be retained longer for analytics.
How Is Third-Party Data Shared or Blocked?
“Forewarned is forearmed.” Data sharing is governed by access controls, with strict permissions, auditing, and vendor agreements; third parties receive only essential data, while blocking mechanisms and revocation options ensure ongoing control and freedom-respecting transparency.
What Remediation Steps Follow a Detected Breach?
Remediation steps after a data breach involve containment, eradication, and recovery; preserving evidence while reviewing misattributed identifiers and access permissions. Third party data handling, data retention policies, and audit trails guide remediation and prevent future breaches.
Conclusion
This analysis binds disparate identifiers into a single, coherent lineage, revealing how access and actions unfold across the data lifecycle. Methodical tracing illuminates layers of authentication, authorization, and movement, like threads in a meticulous tapestry. By mapping events to each identifier, the review crafts a transparent, auditable heartbeat for governance. In this quiet, exacting diligence, risk signals become motifs—recognized, contextualized, and managed—ensuring trustworthy access within a controlled, observable environment.




