Account Data Review – PreĺAdac, екфзрги, 18552099549, 8148746286, 3237633355
The account data review for PreĺAdac and associated identifiers is presented as a structured examination of records, logs, and policy controls. It emphasizes core identifiers and contact vectors as locating mechanisms, then asks whether data accuracy is verifiable, discrepancies are resolvable, and resolutions are auditable. Governance and risk considerations are framed as guardrails for safety and usability. The implications for privacy, accountability, and governance remain unsettled, inviting scrutiny about what gaps may persist and what comes next.
What Account Data Review Really Covers and Why It Matters
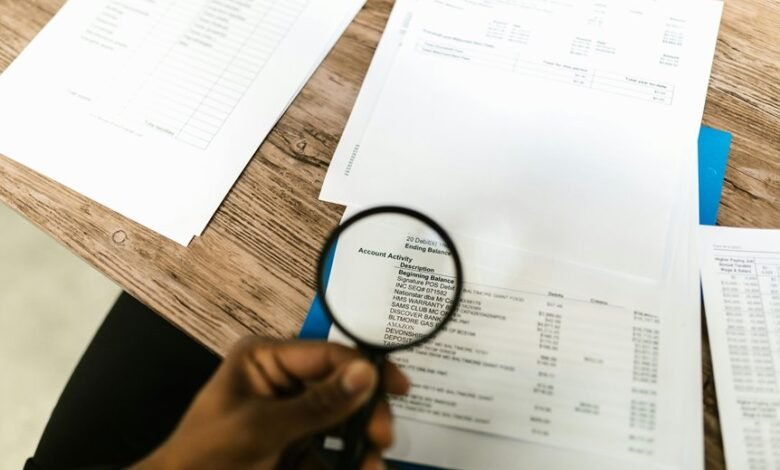
Account data reviews encompass a structured examination of an account’s factual records, transaction history, access logs, and policy compliance.
The scope clarifies data privacy implications, reveals gaps, and tests alignment with stated governance.
It assesses risk exposure, controls effectiveness, and accountability.
Marketing metrics may be reviewed to ensure consent and ethical use, guarding autonomy while preserving operational clarity and freedom.
Identify Core Identifiers and Contact Vectors You Rely On
To identify core identifiers and contact vectors, the review catalogues the specific data elements that uniquely and reliably locate an account: user IDs, email addresses, phone numbers, device fingerprints, and security questions, along with any secondary channels used for verification.
The assessment emphasizes identifiers governance, contact vectors, assessing redundancy, resilience, and potential leakage, without assuming flawless integrity or universal applicability.
Step-by-Step Data Verification: Accuracy, Discrepancies, and Resolution
In the preceding discussion, core identifiers and contact vectors were cataloged to locate an account reliably. Step-by-step verification assesses accuracy methodically, highlighting discrepancies without bias. Data privacy concerns constrain data exposure, while system authentication confirms source integrity. Each mismatch prompts precise reconciliation, documenting evidence, cross-checks, and resolution decisions. The approach remains skeptical yet disciplined, prioritizing verifiable corrections over assumptions to preserve usable, trustworthy records.
Governance, Compliance, and Risk: Keeping Data Safe and Usable
Governance, Compliance, and Risk scrutiny focuses on aligning data stewardship with formal controls, ensuring that policies, procedures, and standards govern data handling across the lifecycle.
The analysis remains skeptical of assumed safety, demanding traceable privacy controls and transparent data lineage.
It weighs risk mitigation against usability, stressing auditable accountability, independent review, and the practicality of enforcement within evolving regulatory landscapes.
Frequently Asked Questions
How Often Should Account Data Be Reviewed for Accuracy?
Data governance favors quarterly reviews for accuracy, with annual audits as a safeguard. It remains skeptical of ad hoc checks while ensuring stakeholder alignment, documenting findings, and preserving objective metrics to support freedom through disciplined, verifiable accountability.
Who Approves Changes to Critical Identifiers and Contact Vectors?
Like a lighthouse in fog, approvals for critical identifiers and contact vectors are granted by designated governance leads after approach alignment and metrics review, ensuring accountability, with a skeptical, objective stance suitable for an audience seeking freedom.
What Data Sources Are Excluded From the Review Process?
Certain data sources are excluded from the review process, as operators maintain selectivities; the review cadence remains steady, with transparent justifications for omissions, while skeptically evaluating provenance, completeness, and potential biases within the overall data sources framework.
How Are Privacy Concerns Balanced With Data Usability?
The approach balances privacy implications with usability by prioritizing data minimization and transparent provenance; it relies on explicit user consent, careful governance, and ongoing audits, yet remains skeptically evaluative of assumed benefits and freedom-enhancing claims.
Can External Auditors Access the Data Review Workflow?
External auditors may access the data review workflow under controlled conditions, with limited scope, rigorous logging, and prior authorization. The process emphasizes transparency, traceability, and safeguards, while preserving organizational autonomy and ongoing freedom to challenge procedures and results.
Conclusion
The account data review consolidates factual records, transaction histories, and access logs to illuminate governance gaps and privacy implications. It identifies core identifiers and contact vectors as locating mechanisms, then scrutinizes accuracy, discrepancies, and resolutions to ensure traceable controls. From a skeptical, objective lens, the process resembles a precision audit: a meticulous telescope scanning for misalignments. When governance and risk controls align with formal policies, data remains usable yet verifiably secure, minimizing hidden risks.




