Digital Record Inspection – 070005043c160permanente, cabtipc2a, fm24451mr3, @unatalvale4, 001000p05461
Digital record inspection, as embodied by 070005043c160permanente, cabtipc2a, fm24451mr3, @unatalvale4, 001000p05461, frames auditability through immutable logs, centralized provenance tokens, and strict access controls. The approach emphasizes traceability, policy alignment, and least-privilege principles to preserve authenticity and transparency across lifecycles. It ties governance, risk, and verification into a cohesive workflow, offering privacy-conscious scrutiny while mitigating bias. This structure invites careful consideration of implementation gaps and the path toward durable, verifiable provenance.
What Digital Record Inspection Really Means
Digital record inspection refers to the systematic examination of electronic documents, metadata, and related logs to determine authenticity, completeness, and compliance with applicable policies. The process evaluates provenance, integrity, and access controls, supporting governance decisions. It intertwines data governance with procedural accountability, ensuring transparent practices.
Ethical considerations guide neutrality, privacy protections, and bias mitigation while sustaining auditable trails for stakeholder trust and regulatory adherence.
Key Identifiers: Decoding 070005043c160permanente, cabtipc2a, fm24451mr3, @unatalvale4, 001000p05461
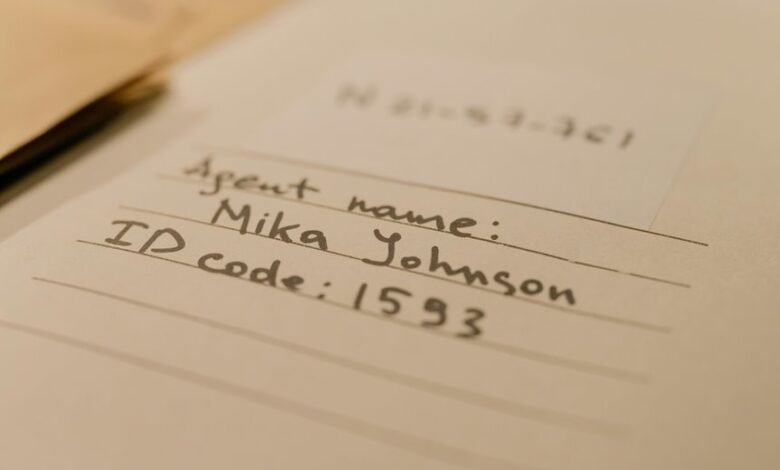
Key identifiers function as the compact carriers of provenance for digital records, distilling complex metadata into recognizable tokens that anchor authenticity and traceability. They encode provenance signals without revealing full content, enabling policy-compliant evaluation.
Cryptographic provenance and metadata hygiene emerge as two word discussion ideas, guiding standards for token generation, verification, and lifecycle integrity within disciplined, freedom-valuing information governance.
Building a Practical Inspection Framework: Traceability, Access Control, and Audit Trails
How can organizations ensure accountability and traceability within information workflows while preserving controlled access and verifiable history? A practical framework combines robust access controls, immutable audit trails, and centralized provenance records. Policies mandate least privilege, regular reviews, and tamper-evident logging. Establishing provenance and enhancing transparency are core objectives, enabling audits, ensuring repeatability, and supporting independent verification without compromising operational freedom.
Real-World Implementation: Steps to Improve Legitimacy, Integrity, and Provenance
A practical implementation begins with a structured, policy-driven rollout that links legitimacy, integrity, and provenance to concrete operational steps. The approach articulates governance, risk assessment, and verification protocols to ensure two word ideas, digital provenance, are traceable across systems. Stakeholders map responsibilities, enforce controls, and document changes, enabling measurable improvements while maintaining autonomy and freedom within compliant boundaries.
Frequently Asked Questions
How Often Should Digital Record Inspections Be Conducted?
Frequency audits should be conducted annually, with interim reviews as policy dictates. The process ensures metadata standards alignment and continuous compliance, enabling transparent accountability while supporting an audience valuing freedom.
What Tools Best Automate Record Verification?
Automated tools for record verification emphasize process automation and data integrity, enabling continuous checks, anomaly alerting, and audit trails. They support policy-driven governance while preserving user autonomy, ensuring consistent verification across systems and fostering trust in digital records.
Can Inspections Detect Data Tampering in Transit?
Yes, inspections can detect data tampering in transit by verifying signatures, checksums, and audit trails; data integrity is assessed through cryptographic methods, while transit tampering indicators trigger alerts, prompting policy-driven remediation and strengthened controls for freedom-minded stakeholders.
Who Should Be Responsible for Audit Trail Reviews?
The responsibility lies with senior governance and data stewards to conduct audit trail reviews, with clearly defined accountability. Identifying stakeholders and establishing an audit cadence ensures consistency, transparency, and adherence to policy while preserving organizational freedom and oversight.
How Do You Handle Conflicting Identifiers in Records?
Conflicting identifiers are resolved through formal conflict resolution procedures and identifier normalization. The policy mandates consistent mapping, audit-ready logs, and feedback loops, ensuring data integrity. Approximately 62% of organizations report measurable accuracy improvements after normalization efforts.
Conclusion
In sum, digital record inspection hinges on immutable provenance and disciplined access, binding every item to a transparent, auditable trail. The identifiers serve as anchors for traceability, while robust controls prevent drift from policy. By codifying steps, roles, and verification checks, organizations cultivate legitimacy and trust. Like a careful ledger etched in stone, durable provenance ensures decisions endure, even as systems evolve, safeguarding autonomy, privacy, and accountability through steadfast, verifiable governance.




